Access Creep
Get in Control of Access Creep
Say goodbye to Access Creep and hello to peace of mind. Join organizations worldwide who have partnered with Gathid to regain control.
Audit User Access Across Any System



























Put the Brakes on Access Accumulation
The constant influx of new hires and role changes are constant in any organization and if unmanaged, result in the accumulation of access privileges that create significant security risks.
‘Access creep’ creates a number of security issues around separation of duties, malicious insider threats, credentials theft, sensitive data exposure and the risk of critical systems breaches.
Gathid isn’t just a solution, it’s your partner in conquering Access Creep. Our user-friendly interface makes it easy for anyone to regain control over access rights.
overview
Access Creep: Solved
Gathid focuses on auditing and analyzing who has access to your systems and critical information.
Our platform conducts comprehensive audits and analysis of privileged access to critical systems and sensitive data, enabling users to efficiently assess compliance across your organization.
Users can instantly assess the health of access compliance across your business and quickly determine where further investigation or remediation is required.
Why you should solve access creep:
- Reduce the risk of malicious insider threat and data breaches.
- Mitigating Access Creep fortifies your organization's security.
- Addressing Access Creep boosts operational efficiency.
- Ensure regulatory compliance (i.e ISO 27001).
- Mitigate risk and boost productivity.
Step 1
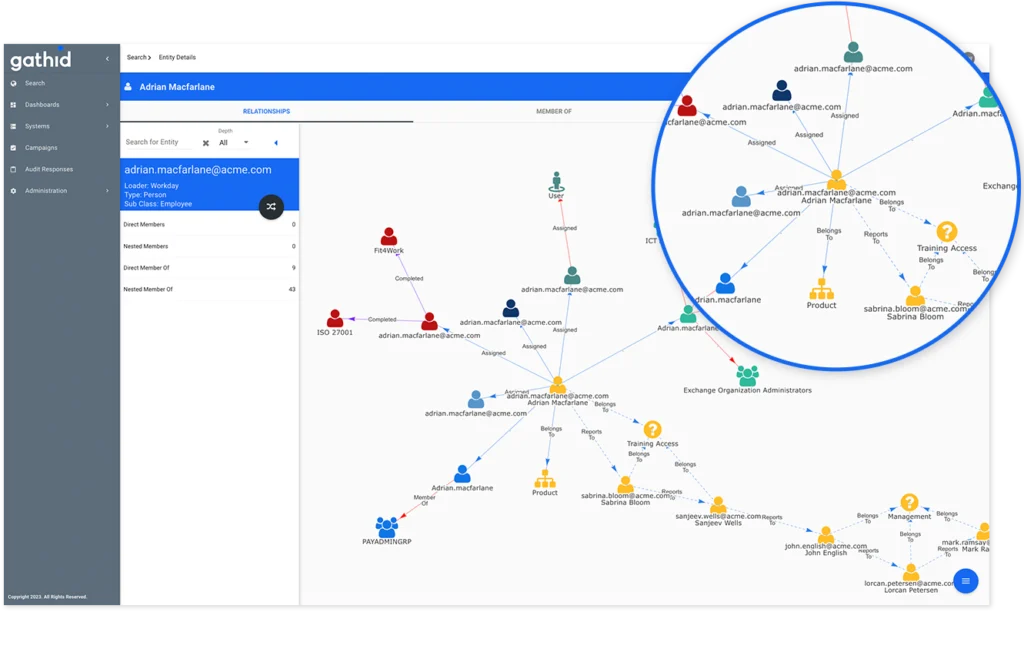
Visualize User Access
Gathid provides a single view of access across your organization. By consolidating access data from various sources, it offers a comprehensive view of who has access to what. This clarity enables you to identify and address access creep effectively, ensuring that only authorized individuals have the necessary privileges.
Step 2
Identify Your Roles
Gathid uses a role-mining process that discovers relationships between users based on similar access permissions, which can logically be grouped to form your collection of roles.
This approach ensures that access privileges align with job responsibilities, effectively preventing access creep and maintaining security.
Step 3
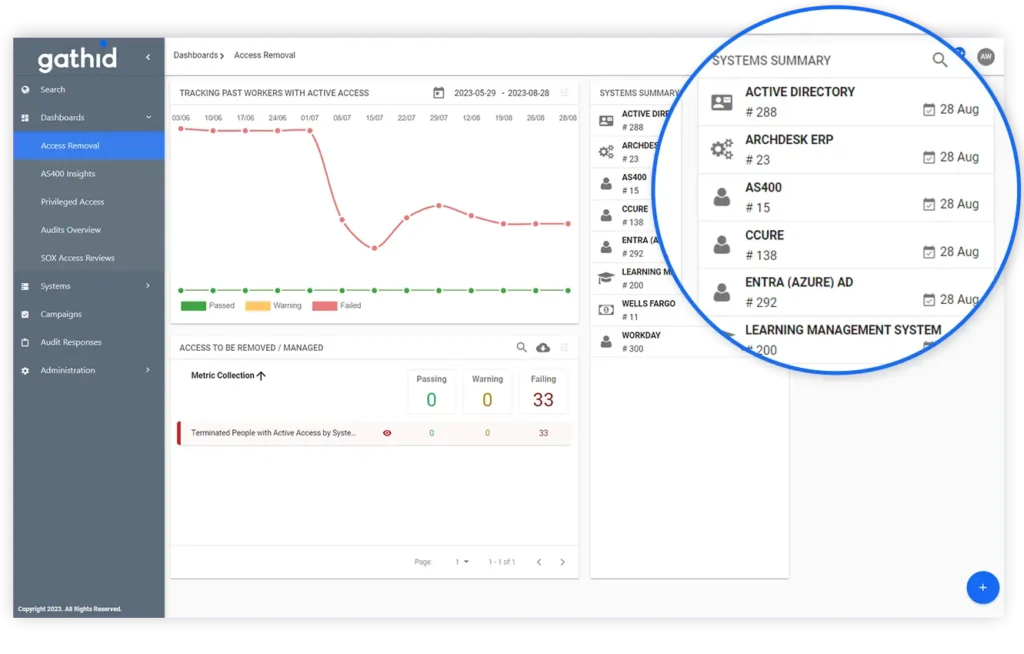
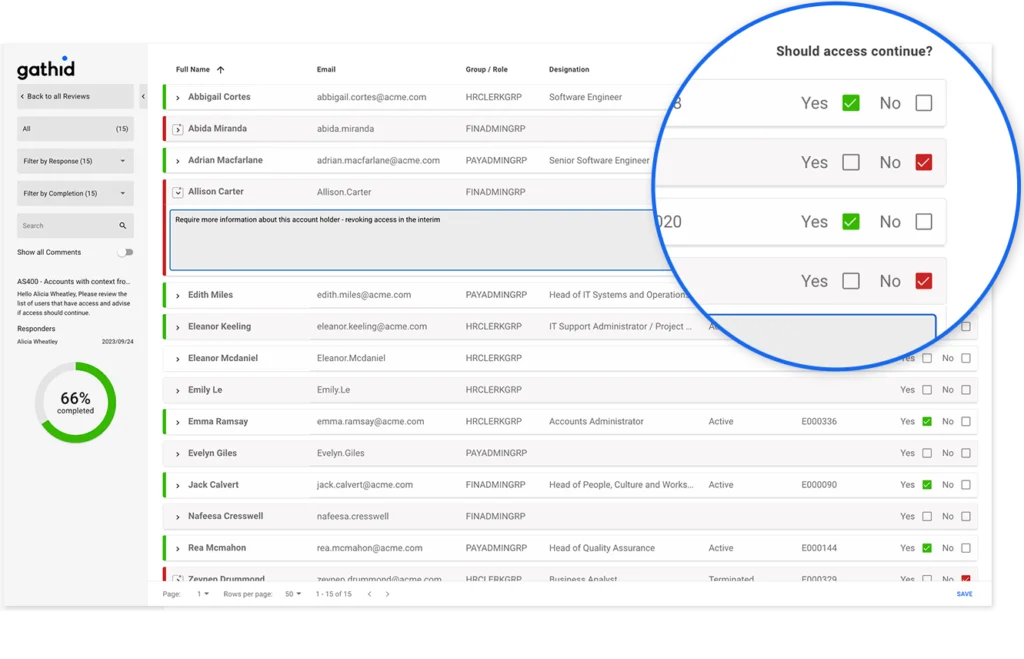
Control Access Creep
Gathid puts a stop to access creep while delivering detailed reporting to determine access continuation.
This helps to improve audit outcomes and allows users to quickly run queries and visualize access for specific systems or groups of users instead of long lead times to get a static report.
Why Choose Us
We do things differently
Our mission is to build the world’s best modeling tool for identity and access solutions. Regardless of where you are on your identity and access journey, Gathid is here to help you to solve complex identity issues in a simple way.
Expertise & Experience
Gathid simplifies complex identity and access challenges with a lightweight, user-friendly solution.
Proactive Approach
Our solution offers a new and fast approach to simplifying complex identity and access challenges.
Solution & Scalability
Gathid is designed to scale with your business, accommodating for growth and changes.
End-to-End Support
We make sure you will receive unwavering support from implementation to utilization.
We collaborate with innovative companies across various industries, ranging from 1,000 to 100,000 employees, who highly value technology and prioritize strong security measures.
Contact Us
Want to learn more about how Gathid can help you to get in control of user access risks? Find out by asking an expert.
Schedule a free 30-minute demonstration.
Connect with a Gathid expert to understand your business needs.
Get new insights on automating and solving identity issues.
Complete Your Details
General Questions
Frequently Asked Questions
Gathid streamlines the decision-making process surrounding identities and their access in you business, providing a solution that helps our clients to verify that only the right people have access.
We redefine identity security and governance with a unique approach. Our cutting-edge patented graph technology, seamlessly connects identity and access system data from all corners of your enterprise – HR, IT, Security, Finance, Business, you name it.
No matter where you are in your identity and access journey, Gathid is here as a game-changing digital identity and access modeling software solution.
Companies typically have more than one ‘source of truth’ when it comes to knowing who is in their workforce. Employees, contractors and students are managed in one or many HR, IT and Accounts Payable systems and across multiple and seperate corporate business units.
Gathid collects access data from groups, applications, legacy systems or files shares. Even your physical and operational technology access data can be monitored.
» Active accounts for terminated staff
» Accounts that have non-expiring passwords
» Account ownership
» Access to file shares
» Role change monitoring
Identity and Access Management (IAM) deployments are often significantly delayed and or fail, due to the complexity in required systems integrations and the rigid requirements of RBAC role definitions.
Gathid offers unique value in the ability to leverage existing files and api connectors to receive read-only identity (HR/IT/Role) and access (Accounts and privileges) data. It rebuilds your IAM architecture every day, allowing you to visualize and track changes automatically.
Gathid is here to simplify and compliment the most complex portions of an IAM implementation.
