Join us at Identiverse 2026. See who and what has the Power to Act across your enterprise >>>
Identity programs stall when role design is based on what access should be rather than what authority actually exists. Gathid gives identity teams a model of real authority — the effective access that exists after every group, delegation, and system relationship is accounted for. This way, role design and cleanup starts from a foundation of truth, not assumption.



integrity in access privileges
An organization came to us after a three-year IAM implementation had stalled at role design. Their team had built hundreds of roles via a complex spreadsheet, but had no way to validate whether those roles matched how authority actually existed in their systems. Gathid modeled their real authority structure in 48 hours. The team found that 40% of their proposed roles needed to be revised before any provisioning could proceed. Role design moved faster in the following month than it had in the previous year.
Roles rarely stay clean. Exceptions accumulate. Mergers add complexity. Systems grow. What began as a well-defined RBAC model gradually accumulates authority that was never intended. Gathid surfaces where roles have drifted from their original scope, identifying identities with effective authority that exceeds their role design, and showing exactly which relationships created it. Teams can remediate with confidence because they can see the structural cause, not just the symptom.

Step 1
Before any role is designed or revised, Gathid shows what authority currently exists across your environment. Identity teams see effective authority, not what was provisioned in isolation, but what each identity can actually do across every connected system. Role design managed from reality.
Step 2
Gathid surfaces roles where effective authority has diverged from intent — where exceptions, delegations, and cross-system combinations have created exposure beyond what the role was designed to carry. Teams can prioritize remediation based on actual risk, not assumed compliance.
Step 3
Once roles are defined against real authority structures, Gathid tracks how they evolve. When authority drifts from role design, through new and updated system integrations, organizational changes, or exception accumulation, Gathid flags it automatically before it becomes a compliance or security problem.

WHY CHOOSE US
Inspired by the power of gathered identities, Gathid pinpoints identity and access anomalies, symbolized by our iconic blue dot. This isn’t just pattern recognition; it’s 20 years of expertise in distinguishing critical insights from the noise to ensure the integrity and security of your identity information across your systems.

Gathid stands out with over two decades of industry leadership, offering unrivaled insights and proven solutions across complex identity landscapes.
Gathid helps anticipate and mitigate identity threats before they arise, ensuring your digital ecosystem remains resilient against emerging challenges.
Our scalable solution adapts to your growing needs, ensuring seamless integration and performance regardless of your organization’s size.
From initial consultation to ongoing utilization, Gathid provides comprehensive support, ensuring your identity governance framework thrives.
We partner with forward-thinking companies in sectors like mining, manufacturing and banking—spanning 1,000 to 100,000 employees —who put a premium on cutting-edge technology and ironclad security.
Contact Us
Struggling to manage a tangled web of user access? Facing security vulnerabilities and inefficiencies due to your accumulated identity debt?

General questions
Gathid streamlines the decision-making process surrounding identities and their access in your business, providing a solution that helps our clients to verify that only the right people have access.
We redefine identity security and governance with a unique approach. Our patented graph technology seamlessly connects identity and access system data from all corners of your enterprise – HR, IT, Security, Finance, Business, you name it.
No matter where you are in your identity and access journey, Gathid is here as a game-changing digital identity and access modeling software solution.
Companies typically have more than one ‘source of truth’ when it comes to knowing who is in their workforce. Employees, contractors and students are managed in one or many HR, IT and Accounts Payable systems and across multiple and separate corporate business units.
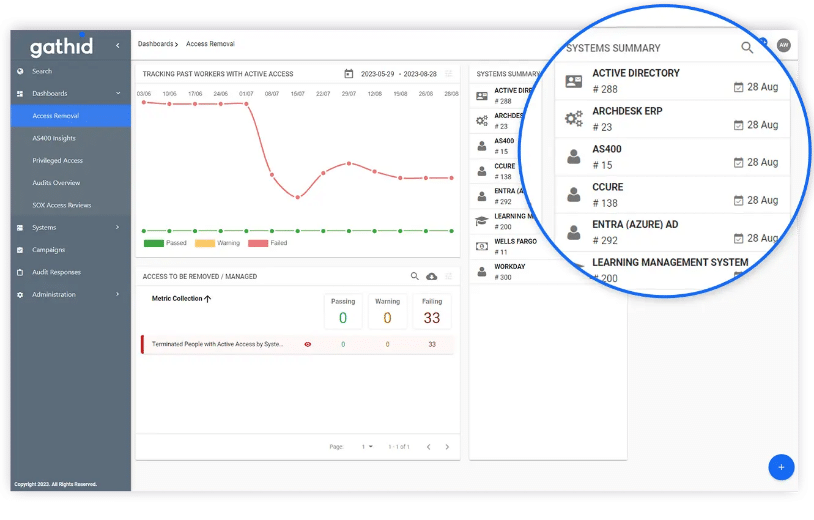
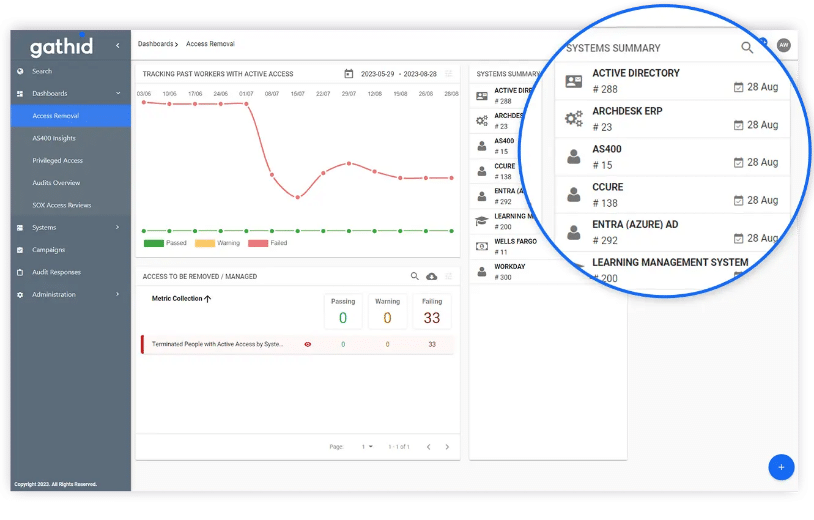
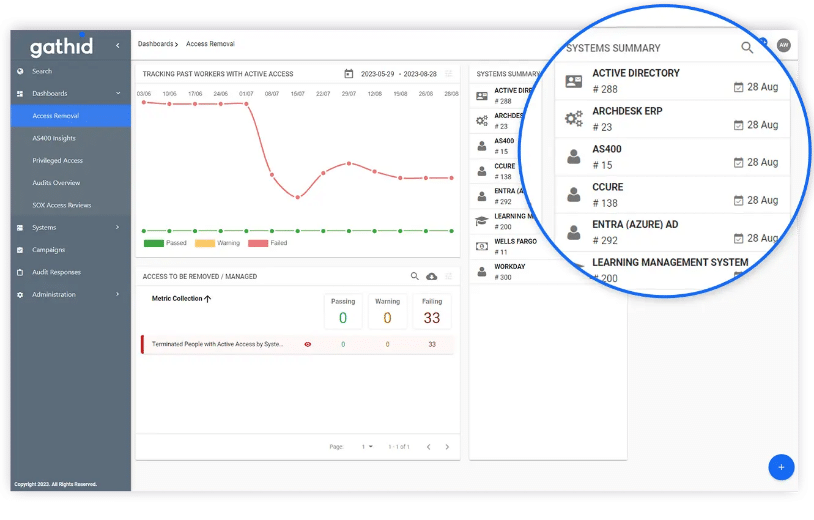
Gathid collects access data from groups, applications, legacy systems or files shares. Even your physical and operational technology access data can be monitored.
» Active accounts for terminated staff
» Accounts that have non-expiring passwords
» Account ownership
» Access to file shares
» Role change monitoring
Identity and Access Management (IAM) deployments are often delayed and miss initial expectations, due to the complexity in required systems integrations and the rigid requirements of RBAC role definitions.
Gathid offers unique value in the ability to leverage existing files and API connectors to receive read-only identity (HR/IT/Role) and access (Accounts and privileges) data. It rebuilds an identity model every day, allowing you to visualize and track changes automatically.
Gathid is here to simplify and complement the most complex portions of any IAM implementation.
User access reviews play a pivotal role in maintaining data security and ensuring compliance. They act as a protective shield, permitting only authorized individuals to access critical data and systems while reducing the risk of data breaches.
With Gathid, our innovative platform automates user access reviews, making the process efficient and accurate. Our system automates your user access reviews and provides precise user access data that you can trust, all from a single source.
